Security Solutions Fight Spam and the Threats It Brings to Local Government
Five years ago, the employees of Alexandria, La., complained a lot about spam. It filled their inboxes and caused constant headaches for IT team members and city workers alike.
Fast-forward to July 2017, when the city received 32,294 emails. Only 3,082 made it to inboxes. Alexandria’s email defense — a SonicWall appliance — quarantined the rest and classified them all as spam. It’s an outcome that keeps virus and malware attacks down and improves user productivity and satisfaction, says Gary Walker, a network administrator for the city.
“Every email is scanned and run through anti-virus programs,” Walker says. “As an administrator, it’s something you have to do. If you don’t run a spam solution in a large environment, you’re asking for trouble.”
Spam presents a problem for a variety of reasons — and not just the obvious ones. Although most spam is simply online junk mail, some carries viruses, malware and malicious links that can take down a network or expose data and applications to theft.
Organizations have seen a decrease in spam over the past few years, but the threat level appears to be increasing again: More than 3,000 spam messages went out every second in 2016, up from fewer than 1,500 a second in previous years, according to the Cisco 2017 Annual Cybersecurity Report.
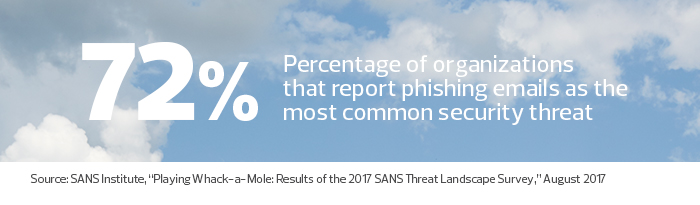
That same study found that 8 percent of spam contains malware, viruses and ransomware. Another analysis, from the Anti-Phishing Working Group, reported that the total number of phishing attacks in 2016 increased 65 percent over 2015. Spam now fools many more people, as hackers become smarter and use social engineering or stolen data to improve open and click-through rates and circumvent traditional email filtering. State and local IT teams must consider new strategies to avoid succumbing to that onslaught.
Hunting Down Hidden Dangers in Spam
Spam often acts as a vessel to trick recipients into sharing personal information or login credentials. “You see a lot of tailored emails that use social media to make them look real, and that’s a problem because very personalized emails are easy to fall for,” says John Pescatore, director of emerging security trends at the SANS Institute, a nonprofit security training and research firm.
Once an employee shares data, attackers can turn an email server into a spam bot, which creates a drag on network productivity and a threat to email reputation. It can affect overall productivity too, if employees spend time deleting unwanted messages or IT gets bogged down in damage control.
Spam and its aftermath can also keep constituents from completing necessary business, says Rishma Khimji, assistant IT director for the city of Reno, Nev. “We don’t want to inconvenience our constituents if someone in a city agency gets hit and they can’t process a tax payment or request a permit.”
Email Filtering Helps Cities Say No to Spam
IT executives use several tools to combat spam and the security threats it brings. Norfolk, Va., which often faces major phishing campaigns, relies on Microsoft Office 365 for Government and boosts its spam safeguards with Microsoft Exchange Online Protection, a cloud-based email filtering service. During a recent attack, cybercriminals sent emails designed to look like they were from the city’s internet provider.
“The emails asked more than 200 employees to provide their credentials so the provider could research a possible security breach,” says Steven DeBerry, the city’s CIO.
While some zero-day attacks like that get through, DeBerry says he’s happy with his program, which uses anti-malware, policy filtering and content filtering to reduce the amount of spam that hits inboxes. “In the past week, the solution captured 90,000 spam messages and 200 emails with malware,” he says.
In Tacoma, Wash., the cloud-based Proofpoint Enterprise Protection with F-Secure has freed up the IT help desk, says CISO Ron Jimerson. Spam-related calls previously inundated the team, which also handled malware that came in via email. The help desk spent countless hours fielding complaints and dealing with the fallout from those who took the spammers’ bait. Tacoma’s Proofpoint solution analyzes sender-recipient relationships, domain reputation, email headers and content to ferret out spam and other malicious messages, keeping inboxes clear.
“Spammers are very smart. We might get a fake email from the city manager addressing the finance manager to make a transfer,” Jimerson says. “Getting rid of that spam gives us a tremendous amount of cost savings.”
Hardware Provides a Proactive Approach Filtering
Some organizations turn to hardware to fight spam, malware and viruses. For example, in Alexandria’s city offices, a SonicWall email security appliance scans all inbound and outbound traffic that uses Simple Message Transfer Protocol, looking at the messages and attachments. The device searches for and isolates anything suspicious, including known and unknown viruses and malware, spoofed email addresses, and blocked domains and IP addresses. Reno uses a hybrid approach — a cloud-based email program with built-in spam filtering as its first line of defense, and a Sophos XG Firewall web gateway appliance as backup protection.
“The appliance lets us see traffic coming in,” says Khimji. “If we see increased packets from a specific IP or sender, we can do smart blocking. We’re now able to get out of the reactive business model and into the proactive model.”
Those technologies, which perform anti-spam and active scanning, can identify whether messages have any malicious intent. They’re also able to do something that previous gateways couldn’t, says SANS Institute’s Pescatore.
“Some of the better gateways will look at traffic and know that a message has a URL in it that is a domain registered a week ago with a personal credit card,” he says, referencing a tactic used by cybercriminals. “They know, based on that information, that the message contains a threat.”











