5 Best Practices for Protecting Your Endpoints
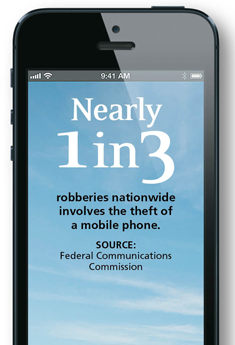
The proliferation of smartphones, tablets and notebook computers in state and local agencies has led to a corresponding rise in the number of lost and stolen devices that must be recovered or replaced. Ensuring that the sensitive data stored on those devices isn't compromised in the interim is a challenge no government IT leader can ignore.
"Governments can't afford to make headlines because of data loss," explains Randy Abrams, research director for the testing and analysis firm NSS Labs. Breaches are embarrassing, but they can also be crippling. One of the best lines of defense, he adds, is a sound endpoint protection strategy.
Endpoint protection tools encompass everything from basic anti-virus and web and content filtering to mobile device management. But there's more to endpoint security than a simple software install.
Government IT leaders who have successfully implemented an endpoint protection strategy recommend the following practices.
Ask Peers for Advice
When the city of Salina, Kan., sought to change anti-virus software providers, its technology team didn't have to look far to find a suitable alternative.
Saline County, of which Salina is a part, had recently implemented Sophos Endpoint Protection, based on the recommendation of the Kansas Information Technology Office. According to Brad Bowers, Saline County's director of information technology, the county uses the solution to secure 300 desktop computers and notebooks for employees in the field and on the road, to scan files and Internet traffic, and for patch assessment.
When Jack Rolfs, director of computer technology for the city of Salina, learned that county leaders were happy with Sophos, he and his team decided to roll out a "small test." The product worked so well that the city now relies on Sophos to provide anti-virus and anti-malware protection for 425 users, including more than 60 public-safety workers with mobile data terminals.
"Finding out what your peers are using and how they like their product is very important," Rolfs insists, noting that Saline County's successful Sophos deployment offered compelling motivation for his city to adopt the solution as well.
"Smaller organizations don't always have the resources to do the research," Bowers adds. Fortunately, the state of Kansas "did the research on this product and shared that knowledge."
Keep an Eye on the Bottom Line
"Dollars can't be the only reason to go with a product," Rolfs says. But cost is important, nonetheless.
In Salina's case, transitioning to Sophos generated a cost savings of more than 50 percent per seat. "If you can get to apples to apples in your comparison, then the dollars have a lot of weight," Rolfs says.
Bowers says Saline County officials also embraced Sophos primarily because of the price, which the state had negotiated. The product's additional functionality was also a factor. Besides Microsoft Windows patch assessment, Sophos performs Adobe and Java assessments, which the county didn't have in its previous endpoint protection solution. "Sophos also has disk encryption, which can help secure devices outside of the network," Bowers adds.
Manage Centrally
The endpoint protection mission in Florida's Citrus County Supervisor of Elections office is straightforward: Centrally manage all devices to keep them up to date and swiftly mitigate threats.
"Endpoint protection is the first thing [we load] onto new computers," says Manager of Logistics and Technology Tim Gunsteens. His solution of choice for the agency's 50 desktops and 10 notebooks is Symantec Endpoint Protection 12. "Everything that comes in — whether it's online or on CD, floppy disk or USB — is scanned," he says.
Gunsteen says he focuses heavily on endpoint protection because he can't ban outright what might be considered "dangerous" applications, including the social networking platforms that the agency's 10 full-time and 60 part-time employees often use to conduct county business.
"With centralized management, I can monitor endpoints closely and force everyone to [accept] regular updates," Gunsteens says. The approach has been successful, in part because the software is quiet, works cleanly and doesn't get in the way of end-user productivity.
"Once endpoint protection is set up and running properly, you rarely have to worry about anything," he adds. "In the past three years, I've spent maybe a couple of hours fixing problems that circumvented endpoint protection."
Allow Room for Growth
Initially, officials in California's Fresno Fire Department thought they would use tablets only to access web applications and perhaps take photos. That changed once fire inspectors had the devices in hand, however. Suddenly, they were completing all sorts of tasks, including writing and uploading citations, fix-it lists and other critical documentation, along with photos, while in the field.
If Paul Pedron, senior network systems specialist for Fresno's Information Services Department, had selected an endpoint protection solution for the tablets based on the department's original requirements, they would have been vulnerable.
For the fire department, providing access to sensitive information in the field requires the ability to locate a lost or stolen device and remotely wipe it if it's compromised or damaged. With Novell's ZENworks Mobile Management (and file upload plug-in), Pedron can do all of those things. The solution allows him to secure and manage not only the fire department's tablets, but also the smartphones and tablets used by the city's parks department, public works, public utilities and retirement board.
Fresno currently has just 120 Apple iOS and Android devices circulating, but Pedron expects that number to reach 750 when the police department completes its rollout later this year. But he isn't worried, he says, because ZENworks makes it easy to set and reset policies as user bases and use cases evolve.
Educate, Educate, Educate
There's no such thing as too much information sharing, particularly when it comes to endpoint protection. "Education for users is sorely underappreciated," NSS Labs' Abrams says. Time spent communicating the importance of diligence now "can prevent data breaches and losses" later, he adds.
By explaining to employees the repercussions of visiting certain sites or sharing certain data, for example, state and local agencies can avoid a lot of problems, Abrams continues. Letting users know that endpoint protection tools monitor and log their activities also can act as a deterrent to malicious behavior.











