3 Steps to Simplify Single Sign-On for State and Local Governments
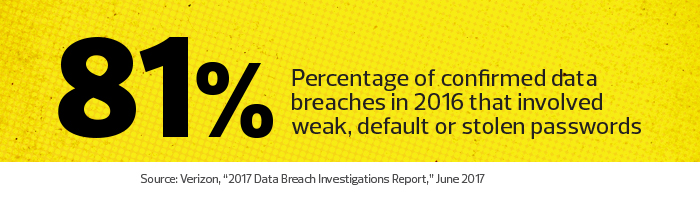
The days when users are required to remember numerous complex passwords may be coming to an end, as single sign-on (SSO) technologies are finally taking hold in state and local agencies. Several factors have brought this about: better technology, a wider selection of identity management tools, lower-cost SSO alternatives and a heightened awareness of massive password breaches.
The creation of digital information portals for citizens to access government services has also bolstered demand for SSO capabilities, as has the increased adoption of Software as a Service (SaaS) products as many agencies migrate to cloud-based applications.
The migration of government infrastructure, apps and services to the cloud has increased the appeal of new identity management controls and capabilities that use SSO software to simplify access for users, helping them to remain productive. Effective access controls enable users to take advantage of government IT systems regardless of the time they choose to work, their location or the device they happen to be using.
State and local agencies should keep several important factors in mind as they consider SSO solutions:
SIGN UP: Get more news from the StateTech newsletter in your inbox every two weeks!
1. Evaluate SSO Tools Strategically
As they decide which SSO tool to deploy, IT leaders should consider the following issues:
Do the agency’s apps support SAML?
Security Assertion Markup Language is the most popular way to automate connections to various SaaS applications. It was originally created to exchange markup language between websites and has become a popular tool to make logins easier among trusted apps and services. Setting up SAML authentications requires some specialized knowledge in this area, but most SSO tools make this process relatively easy, provided the apps in question support the protocol. If an agency’s custom apps don’t support SAML, other mechanisms may be needed to automate user logins.
Can the agency implement risk-based authentication, multifactor authentication or per-app authentication?
All of these have the ability to make sensitive apps more secure across an agency. They also deliver significant flexibility and the ability to trade security for ease of use.
2. Take Steps to Improve Agency Directory Management
Keep the agency’s Microsoft Active Directory (or other directory services) up to date. Users come and go from state and local networks, and servers and services are frequently added and subtracted. Trying to keep track of these changes is difficult, and in many shops, directory information gets outdated and stale. In such an environment, SSO can be less useful.
Consolidate user directories. When agencies have multiple user directories, SSO tools can help consolidate and synchronize them.
This can minimize IT support costs and prevent nonsecure or unauthorized users from gaining access to networks and apps.
3. Optimize Use of Features that Minimize Demands on IT Staff
Automate user provisioning and onboarding, and facilitate self-service user operations. When a new user is hired, SSO tools can make him or her productive from day one with the right access to the entire fleet of agency-approved apps. SSO tools are also a key player in self-service end-user portals, whether for agency users or for citizens who want to access government services. Neither group wants to wait on IT staff to be activated, onboarded, installed or supported. They just want to log in (only once, please!), download their apps and get started. The SSO technologies are a key enabler of the self-service portal.
Have more granular application access controls. With SSO tools, agencies can more finely tune their application access across workgroups for additional security benefit. They can also revoke application access automatically once a team is finished using a particular app.
SSO can also help agencies shore up security defenses. Find out more here.











