Bug Bounty Programs Can Help Local Governments Stamp Out Security Threats
Security experts face a major challenge in dealing with skilled hackers who continuously try to gain access to state and local IT systems. These hackers, who spend years building their cybersecurity skills, often discover previously unidentified vulnerabilities in a website and exploit them to steal sensitive information or damage the site.
But what if security teams could get these hackers to work with them, rather than against them? For years, private sector organizations have sought to harness the skills of these individuals, offering them the opportunity to use their powers for good, rather than evil, through the use of bug bounty programs. Federal agencies are starting to get in on the game, and the opportunity is ripe for state and local governments to follow suit.
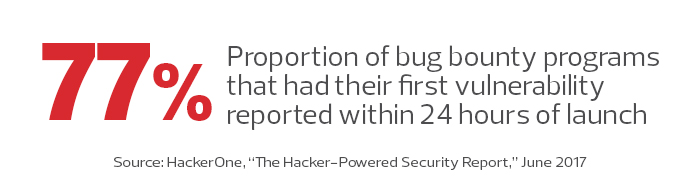
Bug bounty programs provide hackers with the opportunity to test their cyberskills against existing sites and disclose their findings to the site's operator, rather than exploiting them for malicious purposes. In exchange for their report, bounty program sponsors offer individuals who discover vulnerabilities modest financial rewards, publicity and the warm feeling of doing a good deed.
Federal agencies have launched several bug bounty programs in recent years, with more on the way. Early efforts were focused within the Defense Department, with widely publicized "Hack the Pentagon" and "Hack the Army" events drawing participants from across the demographic spectrum and identifying numerous vulnerabilities in government systems. The Pentagon program wound up paying out more than $70,000 to security researchers who submitted validated vulnerabilities.
State and local agencies seeking to establish a bug bounty program can learn from the examples set by federal agencies and private industry. Following a few best practices can help state and local agencies improve their results.
Set the Program Scope Clearly
Before setting hackers loose on agency systems, bug bounty programs should clearly define their parameters. What specific systems are covered by the program, and which are off-limits to testers? The "Hack the Pentagon" program reduced risk by requiring testers to preregister with the government, subjecting them to security screening, and then limiting their activity to static websites that did not contain sensitive information. The Army's follow-up program raised the stakes (and the potential reward) by bringing into the scope dynamic websites that process personal information.
It's best to start small. Agencies should create a program that focuses on one clearly defined target that is isolated from other systems and represents low risk. This approach allows agencies to get the hang of running a bug bounty program and consider moving to more sensitive systems once they have the kinks ironed out.
Agency cybersecurity teams should also step up monitoring of systems outside the scope of the program to watch for rogue attackers.
Define Technical Rules of Engagement
Agencies should also clearly lay out the technical rules of the road. For example, most bug bounty programs specifically prohibit the use of denial-of-service attacks against testing targets. Flooding an agency with fake network traffic is a great way to take other systems offline and prove the obvious — that bandwidth is a limited commodity.
Similarly, bug bounty programs should set forth basic principles to guide testing activity. Participants may be required to disclose vulnerabilities to the agency promptly and be prohibited from releasing information to the public or third parties until the agency has remediated the issue.
Participants should also be warned that they may not exfiltrate data from target systems or intentionally cause damage to systems during their tests. Agency cybersecurity officials should play a key role in defining these rules.
Respond to Submissions Quickly and Keep Submitters in the Loop
Government security professionals should keep in mind that most participants in bug bounty programs aren't in it for the money. After all, they're usually competing for a modest reward of a few thousand dollars. Participants really crave both recognition and the satisfaction of helping to improve cybersecurity. Acknowledging that, agencies should design programs to provide prompt and regular feedback to participants who submit vulnerabilities, as well as public recognition of significant discoveries.
The "Hack the Pentagon" program set out clear expectations for communication. DOD stated that it would, to the best of its ability, confirm the existence of submitted vulnerabilities to the submitter and keep the submitter informed as it worked to fix the problem. This type of disclosure goes against the grain for many security professionals, but it boosts the morale of participants and encourages them — as well as the rest of the security community — to continue in the program. If submissions seem to go into a black hole, word will spread quickly and researchers will stop participating in the program.











