What is Degaussing & Why Isn’t Always Effective
When Microsoft announced plans to stop supporting Windows XP, it forced many governments to buy new notebook and desktop computers. That means they’ll also be spending a lot of time and money decommissioning the old hardware.
Degaussing is a commonly used method for wiping storage data because it’s fast. But unlike shredding, there’s no visual feedback to tell whether everything is gone.
“Because it disables the media, there’s no way to easily check [the quality of the data deletion],” says Michael Cheslock, vice president of technology and sales at DestructData. “Your only quality-control option is to send it to a forensic lab and have them sample drives that you’ve degaussed. That’s usually $200 to $500 per drive.”
Although the degaussing itself is fast, the prep work is not. If hundreds or thousands of notebooks, workstations or servers have to be decommissioned, labor costs will quickly mount, as will security risks due to rushing.
“The process of degaussing a hard drive, depending upon the type of degausser used, may involve careful disassembly or unpackaging of the drive or other manufacturer-specified procedures,” says Victor Cuco, MindPoint Group senior consultant. “There is some risk in not properly executing procedures, especially in high-volume environments. The NSA also recommends physical destruction of a hard disk drive after degaussing prior to its release outside of an organization’s control.”
Software that overwrites the data multiple times is an alternative to degaussing that’s worth considering if the PC needs to be reused by another employee or if it’s being donated to charity.
For all wiping techniques, make sure that chain of custody isn’t broken. Stacks of notebooks awaiting decommissioning are tempting for thieves and hackers.
As a hacker, “you have limited exposure to data in motion and data at rest,” Cheslock says. “But if you get access to end-of-life or end-of-service media, you have unlimited time to attack it.”
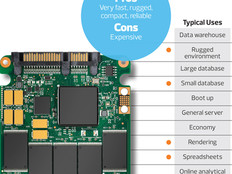
Solid-State Drives Create New Challenges
Tablets — and increasingly, PCs — use flash memory instead of hard drives. That creates different considerations when it comes to securely decommissioning those devices. For example, even if degaussing destroys some of the media’s electrical aspects, the data is still there.
“If overwriting is selected, then software traditionally used to wipe magnetic hard-disk drives can also be used for flash media/EEPROM,” Cuco says. “Even the NSA accepts a special overwriting procedure, which, in addition to types of physical destruction, is an approved form of media sanitization.
“NSA’s procedure involves overwriting using a nonsensitive pattern and then verification that the entire drive has been overwritten with this pattern. For organizations that desire this level of security, careful evaluation of overwriting software capabilities is recommended.”
Others caution that solid-state drives (SSDs) have unique features that make them difficult to wipe completely.
“SSDs have a reserve area on them that is used to load-balance across SSD memory cells,” says Ivan Galic, chief of the enterprise applications and solutions for Montgomery County, Md. “This SSD reserve area can also be quite large and may not be visible to operating systems. Most problematic, this reserve area may contain confidential and proprietary data. At this time, data security on SSDs can only be ensured by physical shredding of an SSD.”
The catch? SSD shredding also has unique issues.
“The NAND chips on the board can easily pop off and fly between the cutters without being physically destroyed,” says DestructData’s Cheslock. “You really need to destroy each one of those NAND chips.
“It’s not that hard to collect data from a NAND chip that’s not physically destroyed. It’s a couple hundred dollars of equipment to read those chips.”
One solution is to use a two-stage shredder, which munches the chips and everything else into pieces smaller than three-fourths of an inch. At that size, recoverability becomes extremely difficult.
Planning Ahead Mitigates Risk and Saves Money
The best time to develop a decommissioning strategy isn’t when hardware has one foot in the grave. In fact, it can be more effective — in terms of both cost and security — to address decommissioning devices at the time of purchase; for example, by selecting OPAL drives, which automatically encrypt themselves from day one.
“People say, ‘I don’t need that much security,’” says Greg Schulz, StorageIO founder and senior analyst. “Fair enough, but those same tools can do the rapid, secure destruction or erase in seconds or minutes versus hours or days.”
One way to determine whether such products are overkill or money well spent is to calculate how many staff hours, plus any specialized hardware and software, would be required to securely decommission those devices another way.
Planning ahead also applies to hosted services. For example, consider having any cloud services contract require physical separation — such as individual disks in an array — between your data and data belonging to the cloud provider’s other clients.
“That’s a function of the storage provider allocating the logical volume intelligently so it’s physically storing it on certain hard drives,” says DestructData’s Cheslock. “If they can’t do that, it tells you they can’t specifically manage it from a media-sanitization standpoint at end of service.”
Five Tips for Securely Decommissioning PCs and Servers
Here’s what Ivan Galic, chief of enterprise applications and solutions for Montgomery County, Md., recommends:
1) Audit and inventory storage media, storage systems, applications and systems that contain sensitive data.
2) Develop, implement and periodically audit policies for media decommissioning and data security. The National Institute for Standards and Technology’s Special Report 800-88, “Guidelines for Media Sanitation,” is a helpful resource.
3) Encrypt data.
4) Use overwrite software that does multiple write passes.
5) Limit access to hardware that’s been decommissioned but not yet sanitized.