Automation, Process Improvements Simplify Patch Management
IT professionals around the world face an overwhelming workload. Buried under a blizzard of help desk incidents, system installations, project work and email, technologists find it difficult to stay on top of the routine maintenance tasks that keep systems secure. Patching is one of the first chores to fall by the wayside.
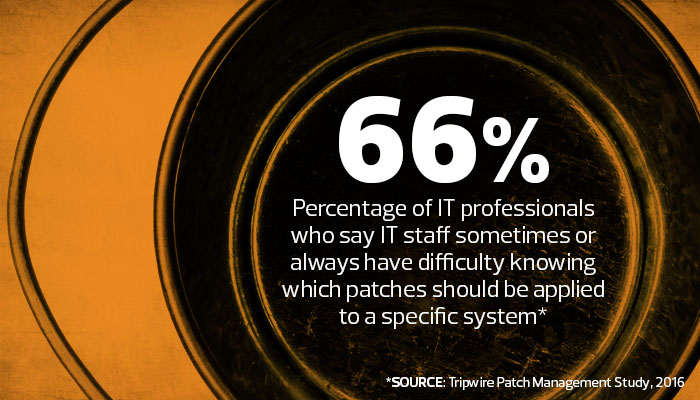
Half of the IT professionals surveyed for Tripwire’s 2016 Patch Management Study say the volume of security patches is either overwhelming or too high to keep up with. While leaving systems unpatched may seem expedient, this disregard exposes government agencies to unacceptable security risks.
Vendors release security patches in response to known vulnerabilities in their products. It’s safe to assume that by the time a vendor learns of a security hole, malicious individuals are aware of it too. That leaves unpatched systems extremely vulnerable to attack, particularly when they have public network exposure.
A quick look at the firewall logs of any government agency will reveal the constant probes of security vulnerabilities from sources around the world. Those scans aren’t focused exclusively on large federal government agencies — they’re just as likely to occur on state and local government networks.
Start with the Operating System, but Don’t Stop There
Administrators seeking to improve patch management processes should begin by building an inventory of the systems they maintain that require patching. Servers and endpoint devices are good places to start, but the list should contain more than computer systems. Network routers and switches, Internet of Things devices, security appliances and practically every other electronic device that connects to a network runs firmware that may need security patches. Consumers everywhere were surprised to learn that even baby monitors demand security attention, after hackers used those devices to spy on sleeping children.
When dealing with computer systems, remember that the operating system isn’t the only component that requires patching. Many of the security vulnerabilities discovered each year exist in the applications that run on those systems. Recent security patches updated everything from Oracle databases to Microsoft Office and Adobe Acrobat. As administrators log patchable systems, they should include all of the software components that require patches and track which systems run each component.
Although administrators may cringe at the thought of creating such a comprehensive inventory for the entire government agency, the task is less daunting than it seems. Configuration management systems can automatically probe systems connected to a domain and develop a list of operating systems and software components used throughout the network, as well as their current patch levels. This inventory not only provides a quick snapshot of the current state of the network but also generates a roadmap for remediation.
Build a Patching Routine
With an inventory in hand, administrators can turn their attention to building a sustainable patching routine. The idea is to create a standard process that takes little effort to maintain but keeps systems continually patched to the most current levels. Automation is the key to successful patching: The more that IT teams can put patching on autopilot, the higher the likelihood that systems will receive patches promptly.
The path to security patch automation starts with research. Visit the support websites for the companies that provide each item on the device inventory and learn their patching procedures. While some vendors release patches on a regular schedule — Microsoft, for example, follows its famous Patch Tuesday approach — most simply release patches when they’re ready. Learn how each vendor issues patches and notifies customers of their availability.
In cases where the vendor offers an email subscription for update announcements, many IT organizations subscribe with an email address that then automatically creates an incident in their IT service management system. Major vendors typically provide this sort of convenient notification service, while smaller companies may just intermittently post patch announcements on a website.
Configuration management systems provide an extremely effective way to automate the distribution of patches throughout the organization. Administrators simply provide the patch to the system and instruct it to automatically apply the patch to affected systems during the next maintenance window. System reports then provide updates on patch status, allowing manual intervention if the updates fail to apply. Deploying patches through configuration management systems saves administrators hours of tedious work, reduces the likelihood of errors and simplifies the lives of overburdened IT staff.
Vulnerability scans also play an important role in patch management strategies. Scanners automatically probe systems on an agency’s network, searching for potential security flaws, including missing patches. Administrators then receive a report summarizing any security issues the scan discovered. The probes provide a valuable cross-check on configuration management reports and sometimes alert IT staff to the availability of patches that they may have otherwise overlooked.
Security patches are one of the most vital defense mechanisms available to government technology professionals seeking to safeguard systems against malicious hackers. Building a solid inventory of systems and applications that require security updates provides a roadmap for automating the mundane work of identifying and applying security patches. The end result is a secure, reliable computing infrastructure that protects the confidentiality, integrity and availability of information assets.











