3 CISOs Weigh In on the Battle for Citizen Data Privacy
Governments at the state and local level must collect a wide range of data; it’s an integral part of the business of governing. And protecting that data from theft is a serious undertaking. In 2017, for example, Texas faced 105 breaches, resulting in the theft of 2.5 million records, according to the nonprofit Identity Theft Resource Center. That represented an increase of five times the records stolen in the previous year.
“I would say that state governments aren’t necessarily any more vulnerable to data theft than other entities or the private sector. Everyone is vulnerable today,” says Amy Hille Glasscock, a senior policy analyst for the National Association of State Chief Information Officers (NASCIO). “The difference is that the government has data on all citizens — it’s not a choice.”
Given the sensitive nature of the data being held (health information, credit card numbers, Social Security numbers, addresses, voter registrations and more), implementing an aggressive cybersecurity framework is critical to thwarting cyberattacks and maintaining public trust. While no single process or technology solution guarantees complete security of citizen data, there are approaches to create the strongest possible defense.
SIGN UP: Get more news from the StateTech newsletter in your inbox every two weeks!
1. Jefferson County Prioritizes Selecting Secure Solutions
In Jefferson County, Colo., CISO Jill Fraser is charged with protecting the data of more than a half-million citizens. Information security at the level of local government can be a daunting challenge, she says.
“I argue it is harder than nearly any other industry. Unlike private sector business, which tends to have a single business focus, local governments have several lines of business, which means our organizations have multiple business priorities,” she says.
The nature of the data presents additional difficulty. “Local governments provide services related to public safety — police, fire, sheriff — and maintain significant amounts of sensitive data,” she explains.
Photography by Willie Petersen
When it came time to upgrade and secure the county’s network architecture, previously built using VMware vShield, Jefferson County Enterprise IT Services identified several key criteria, the most important of which was their desire to implement a zero-trust network model.
“We also decided that vendor lock-in was something we would avoid. If we wanted to change hardware or software vendors in the future, the network solution we chose would need to support that,” Fraser says.
Plus, the county wanted to avoid the purchase of additional hardware to implement the solution. Given that, the team chose VMware NSX. In addition to meeting the county’s identified needs, NSX allows Jefferson County to integrate other security solutions, including agentless anti-malware and host-based intrusion detection and prevention systems.
2. San Diego Emphasizes Communication and Collaboration
As essential as the right cybersecurity tools are to protecting citizen data, technology alone is not enough. Glasscock emphasizes the importance of communication.
A CIO or CISO, she says, “often serves as a translator of sorts in their dealings with nontechnical stakeholders — so good communication skills are vital.”
Darren Bennett, CISO for the city of San Diego, agrees. Bennett manages several petabytes of data for more than 40 departments and partner organizations, spread across 24 independent computer networks and 40,000 endpoints.
While he spent a good deal of time looking at the pros and cons of various cybersecurity technologies — integration with current solutions, cost and adaptation to new threats over time were key benchmarks — Bennett stresses the importance of interdepartmental communication.
“Security is no single person’s responsibility; it takes a team to keep San Diego safe,” he says. “After all, it only takes the actions of one person to make the system vulnerable and jeopardize information.”
“Conducting normal cyberhygiene is critical to eliminating and mitigating possible threats,” he adds.
Collaboration with outside entities is also crucial. “I am active in both public and private organizations and collaborate with information security professionals, research entities, state and federal government sectors and commercial industry peers to continuously refine our security measures and protect the data against the most pervasive attacks,” Bennett says. “It takes a combination of great tools and strong partnerships to be successful.”
3. Fairfax Leadership Finds Strong Cybersecurity Funding
A solid cybersecurity program requires governments to invest sufficient funds. Once again, success can come down to the skill with which CIOs and CISOs can communicate the threat and what is needed to combat it.
Fairfax County, Va., CISO Michael Dent protects the data of over 1.5 million county residents. He employs a defense-in-depth strategy that relies on no single technology.
“We have multiple best-in-breed cybersecurity tools,” Dent says. “We perform above-standard cyberhygiene by having a change control board, patch management process, incident reporting process and a security awareness program.” When it comes to ensuring he has the funding needed for this approach, Dent finds that he can’t sugarcoat the risks.
“Fairfax County leadership gets cyber,” Dent says. “As long as I have been able to brief them and show them a strategy, we have not had issues getting funding.”
With the backing of the county’s leaders, Dent’s team has been able to implement solutions such as Splunk for monitoring and advanced email threat protection and Citrix for remote access to resources.
“All of our endpoint logs and critical data are fed into our security information and event management system, which is configured to alert and provide some automated remediation for the engineers who have to react and defend against attacks,” Dent says.
Having a strategy that can be effectively communicated is incredibly important at all levels of government, according to NASCIO.
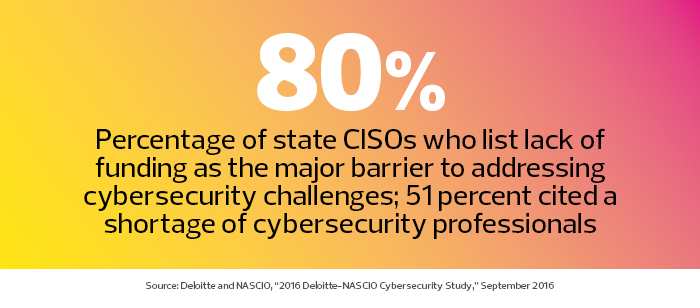
“In our 2016 Deloitte-NASCIO Cybersecurity Study, we found that states with a formal cybersecurity strategy were more likely to get the funding and talent they need,” Glasscock says. “This is significant because lack of adequate funding and lack of workforce talent are major barriers to cybersecurity in state government.”
Protect Citizen Data with Strong Cyberdefenses
The threat of citizen data theft is real, but Fraser is confident that local governments can rise to the challenge.
“I believe locals are poised to be the leaders in government security. We have much supporting our ability to significantly mature our security posture,” Fraser says.
“Local governments are filled with personnel who genuinely and deeply care about the work they are doing. By training our workforce on security practices, local governments can turn a security team of none into a security team of hundreds or thousands,” she says.
Glassock has seen positive developments at the state level.
“Governors and state officials are paying more attention to cyber risk than they have in the past,” she says.











