Local Governments Need Governance and Training Amid IT Security Risks, Study Finds
As local governments use more digital technology, they need to become more proficient about using technology and more vigilant about monitoring security risks posed by their IT systems and applications, according to a study from Rutgers University.
The study, produced by the Bloustein Local Government Research Center, says that local governments face more than cybersecurity risks and actually need to confront six different but interrelated risk areas: cybersecurity, financial, legal, operational, reputational and societal.
Becoming Proficient, Managing Risks
“While cybersecurity (data and personal information theft, and denial of access in particular) gets the lion’s share of public attention, those responsible for managing their organization’s technology face a range of other risks affecting their organizations, employees, customers and clients,” the report states. “What we do and use carry risks. Organizations face risks created by their use of technology. When it comes to using digital technology, cybersecurity is high on the list, but it is also essential to consider and plan for operational, legal, financial, reputational, and society-driven liabilities and exposures.”
The report notes that while the six risk categories for local governments “cover the range of risks, the specific risks that fall under each one may overlap and intersect (i.e., cybersecurity risks can also involve financial, operational, and legal risks), and will evolve (i.e., the assessment of risks related to drone technology is in its infancy).”
Government agencies approach risk management in different ways, and some may have more mature approaches than others. Additionally, governments need to deal with the fact that residents increasingly expect “24/7 access to government information and services, on mobile devices, without regard for how government develops, manages and pays for that access and those services.”
The report says that local governments need to become “technologically proficient” in order to “identify, assess and manage technology risks.” There are four different ways that local governments can achieve this goal, the report notes.
Organizations need to have “technology governance that is driven by senior elected and appointed officials;” and have “planning that is integrated with governance and budgeting;” ensure that “cyberhygiene” is something all employees practice to ensure security; and develop the “technical competency that is needed to drive the management and delivery of the organization’s technology.”
Having a Plan and Carrying It Out
In addition to making sure senior local government officials and IT managers are vigilant about technology security risks, organizations need to have a plan for how to manage risks, Marc Pfeiffer, assistant director and senior policy fellow at the Bloustein Center, told The Daily Targum, the university’s student newspaper.
Pfeiffer told The Daily Targum that when a government agency has a plan it can figure out what technology it is using, create priorities based on those technologies and handle the associated risks and budgets.
Local governments also need to institutionalize cyberhygiene, the Bloustein Center report says. The Center for Internet Security, a nonprofit organization that is “dedicated to enhancing the cybersecurity readiness and response among public and private sector entities,” defines cyberhygiene as “making sure we are protecting and maintaining systems and devices appropriately and using cybersecurity best practices.” The Bloustein study says, “agencies must train their staff, and training cannot stop after one in-service workshop, as the threats keep changing.” Local governments “must require initial and ongoing training.” “Cyberhygiene training teaches employees to identify potentially damaging emails and learning about recognizing 'social engineering,' where people send emails or make phone calls to convince users to take insecure actions," Pfeiffer said.
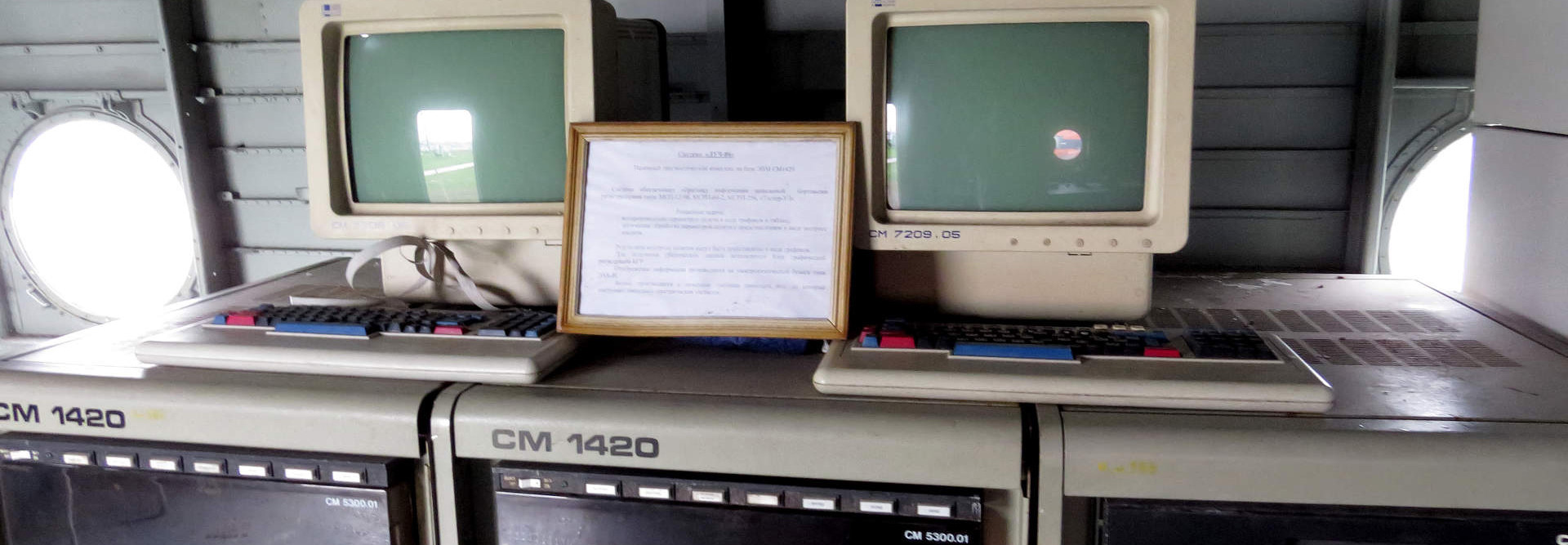
The Bloustein Center report stresses that local governments need to develop ”technical competence” in multiple ways. First, they need to ensure that “all technical aspects of maintaining networks, servers, desktops, laptops, tablets, handheld devices, dedicated appliances, operational technology and process-related equipment are installed and maintained securely in accordance with sound practices.”
Additionally, governments need to ensure “that goods and services are purchased efficiently and effectively, budgetary needs are met, staffing is sufficient, employees have appropriate certifications and keep their skills up-to-date. It also means that open source resources are considered, managed services are used as relevant, and new software needs are met through careful consideration and review.
“In addition, all application development must use contemporary standards and be expertly managed (i.e., the developers use agile development practices), desktop and user support needs are met, service contracts are managed, and specialized needs are addressed.”