5 Best Practices for Agencies to Implement Network Access Control
Providing access to services for a wide array of people can prove daunting for government organizations at all levels. Employees, contractors, visitors and third-party suppliers all require unimpeded access to critical network infrastructure, but they also present potential vulnerabilities. How might state and local government offices meet these demands while ensuring privacy, confidentiality and compliance?
As the risk of breaches grows, so too does the demand for network access control solutions to mitigate the risk. NAC solutions are intended to ensure that only endpoint devices in compliance with security policy can access specific network resources. However, implementing NAC in a world of increasing third-party access and a growing number of endpoints — including BYOD and the Internet of Things — requires special attention to detail. NAC best practices can help state and local governments stay ahead of the curve.
SIGN UP: Get more news from the StateTech newsletter in your inbox every two weeks!
The Perils of Open Access on Government Networks
Governments want to ensure that all users — employees, contractors, constituents and other guests — have unfettered access to the resources they need. But problems abound. In a BYOD environment, many unvetted (and potentially unsecured) devices access the network daily, perhaps inadvertently bringing malware. Hackers welcome openness as they constantly probe government applications and services for vulnerabilities. They also use phishing attacks to steal credentials and infiltrate networks.
Government breaches may be more serious than commercial breaches because they often involve personally identifiable data such as names, addresses, Social Security numbers and birth dates. While a credit card breach can be serious, a person can cancel a card; changing an SSN is a different story.
And the results can be costly: A South Carolina Department of Revenue breach compromised the data of 6.4 million individuals and businesses. One of the largest breaches in history, it has already cost the state more than $25 million, with lawsuits continuing to unfold.
How NAC Has Evolved for Today's Environment
Early NAC technology aimed to curb the spread of malware by preventing infected computers from accessing the network. Built for tightly controlled environments, these tools required endpoints to have specific OS versions and software agents before granting network access. Unfortunately, these older NAC solutions were cumbersome and expensive, and they failed to gain widespread acceptance.
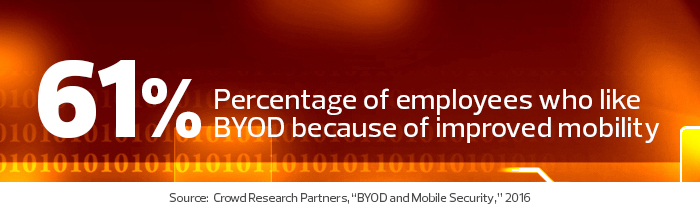
Today, the popularity of BYOD has renewed interest in NAC. Modern NAC tools can easily handle secure access for a multitude of device types, models and OSs — even those beyond the reach of the organization’s enterprise security software, which has proved especially useful in managing guest and contractor access.
For organizations implementing common security controls, NAC serves as a preventive by enforcing rules governing authorized devices and connections. It can monitor adherence to policy, block access or even remediate endpoints and solve configuration issues.
Today’s NAC can help ensure a safe, productive and compliant government computing environment. The following best practices can help state and local IT teams to limit guest access, ensure compliance and provide a frictionless experience for users.
1. Research NAC Solutions Before Purchasing
Look for a NAC solution with an extensible framework that can gather information from a variety of sources, including new devices on the market. The solution should offer a guest portal with limited access and user self-service. Review your network access control policy to ensure it limits full network access to enterprise-owned devices and requires mobile device management to enforce encryption, screen locking and other security settings. The policy should cover NAC integration with other security systems, such as security information and event management.
2. Build a User Baseline and Watch for Changes
Determine how many devices are connected to the network, what type and who owns them. If you don’t know, NAC can provide visibility to existing infrastructure and alert you to new devices. Specify which level of access is available for guest and contractor devices. Once you have built a baseline, monitor changes.
3. Establish Controls for Guests on the Network
Set up guest networking boundaries, including time and location fences. Use NAC to limit guests and contractors, as well as users with personal devices, to protected areas of the network. Roll out major changes, such as quarantine networks, in pilot or monitoring mode. Be sure to educate users about such changes and remediate systems to accommodate them. Conduct a full NAC rollout in phases, culminating in full enforcement.
4. Train IT Staff to Monitor NAC Alerts
Make sure your IT staff is proficient at interpreting NAC alerts to ensure that network access is delivered securely, with minimal disruption to legitimate users. This may be a full-time job, depending on the number of endpoints. If it’s a part-time job, allocate a specific time for the IT team to do the monitoring.
5. Prepare for Network Access Audits
Make a habit of regularly producing and reading historical and real-time reports, so you are ready for an audit. NAC can prove invaluable in arming you with proof that you are controlling and monitoring your network, as well as managing the introduction of rogue devices and restricting access to important information.











